The Internet of Things is a definite revolution in its own right, but it is also part of something bigger: the Internet of Money. The first real "Big Data" collection was/is financial: stock trades, money markets, consumer debt. It all got stored on computers. That led to things like Flash Trading, Mortgage Backed Securities and, more recently, BitCoin and its siblings. Some of it bad, some of it good, mostly just changes brought about by the increasing access and automation of data without any moral compass beyond "it'll make things easier (and there are fees to earn.)"
From Funnel to Cycle
The Internet of Things fits in here because it starts to expand automation from data automation to thing automation. Which is why we're all excited about it. But for the companies that are investing in this buzzword, it goes beyond making it easy for you to set your thermostat or have the lights come on when you open the door. All of that is the hook. Ultimately, they want to automate your purchase decisions.
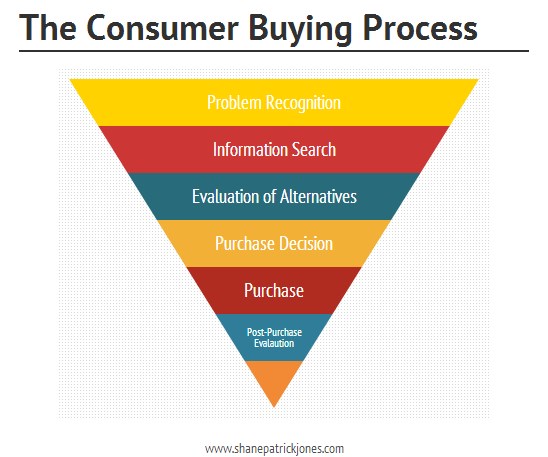
This has already been massively accelerated due to the internet. If you look at the pre-internet consumer decision journey, it is a funnel:
With the rise of the Internet and, more importantly, recommendation engines (based on individual buying data = big data), this turned from a funnel into a cycle:
Recommendation engines operating on the "If you like this, then you'll like it again and also things similar to it" mean that we consumers no longer have to start at the top of the funnel for each and every purchase, but can work within a trust circle (that inner, smaller loop.) But we still have to make the purchase every time. We have to actually click on "Add to Cart."
From Cycle to Out-Of-The-Loop
The big change to the Internet of Money brought on by the Internet of Things is that now, the cycle only needs to happen once. Instead of us making that lower re-loop when we need to replace something, the purchase has already been made and we no longer have to be part of the loop.
This has been going on in industry for a while. "Just in Time" inventory (keeping only enough parts in stock to last a re-stocking cycle) is a similar process, but had purchasing agents involved. The newer system that everyone from retailers to manufacturers to restaurants have been working on for the past two decades is to connect their inventory management systems together, allowing purchase orders to be automatically sent out when inventory reaches a critical state.
Here's Where You Come In (Or Not)
What smart home manufacturers want is to
create a similar inventory management system for your home. If your home system knows when you are low on milk (through your smart refrigerator,) then it can order more and have it sent to your home. It gets charged to your registered account (plus shipping and tax and a fee) and you can cross off a thing you no longer have to worry about. In theory, the fee is less than the gas that you would use to go get that same milk.
All of this assumes that you have a smart appliance, that you take the time to teach it your tastes in various brands, that it won't start recommending other brands (or simply ordering them) because of some kick back between the various milk cartels, that you have consistent power and a solid internet connection. Then, after all of that is set up, you won't have to worry about buying milk ever again.
What a world.